Only recently the phrase ‘digital transformation’ seems to have rescinded its title of most overused buzzword to ‘unprecedented’.
Businesses realise the need to digitise their processes to improve efficiencies, but often underestimate the scope of these projects, and the level of consideration and planning required to ensure successful adoption of new technologies.
The team at TechSpecialist recently completed a large digital transformation project, so I thought it a pertinent time to reflect on how businesses can set themselves up for success when undertaking a similar process.
Typically we’re engaged by clients who have identified most of the following issues:
- In-efficient business processes
- Manually handling
- Lack of automation and visibility
- Poor quality collaboration
While these issues are important to address, the data and insights that are collected as a by-product of the creation of digital assets that can be traced, tracked and versioned often become the most useful in increasing business efficiencies.
Key IT processes to address
- Identity and access management
- File storage repository
- Call centre integration
- Security upgrades for cloud-based software
Identity and access management
While it may not be the sexiest IT process, efficient identity and access management is a key area to address in configuring an organisations systems to ensure smooth day-to-day operations.
The average number of different platforms enterprise level employees will login to each day is between 20 and 30. Expecting users to maintain an acceptable level of password hygiene across this many systems is just not practical.
The most secure and efficient way of combating this issue is to enable a SSO (single sign-on) that federates account details from multiple systems using multi-factor authentication.
File storage repository
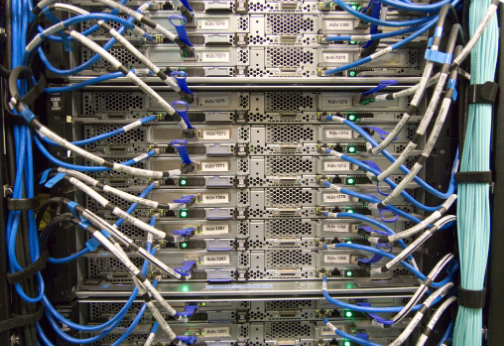
A key component of any digital transformation project should include a move towards cloud-based storage systems to hold data in a central, secure location that can be accessed remotely.
This not only reduces the need for businesses to purchase and maintain their own servers, but allows for increased security and better collaboration. Multiple users can access documents simultaneously and make changes which will be displayed across the organisation in real-time, with increased possibilities for version control.
Data Loss Prevention (DLP) is also made possible using cloud-based storage, using business rules to classify information so that unauthorized users can’t accidentally or maliciously share data.
Contact centre upgrades
Integrating your contact centre with your CRM through a voice platform system allows you to push call data to a customers individual profile, and bring up their service history, which enables the delivery of a highly personalised service.
Before the call is taken, the voice platform will identify key information about the caller, and use business-defined rules to route the call to whoever will be best placed to service that customer’s needs.
The platform also uses AI to understand customer sentiment by analysing voice tone and speech patterns to rank call quality and create a sentiment score. They can be further configured to create alerts in real-time so supervisors can listen in and even intervene on a call if a predetermined sentiment score is reached.
Security upgrades for cloud-based software
On premise SOC and Siem technology is largely considered to be the most effective system for threat monitoring and breach prevention, however until recently the use of cloud-based storage could limit its effectiveness.
Now there are products available that have access to the cloud that can monitor threats and provide an external view of what’s happening within the organisation’s tenancy, which can stop breaches including threats caused by masquerading users.
How to ensure success of your transformation
Ultimately the success of these projects boils down to how well the new systems and processes have been adopted at every level of the organisation, not just by IT.
It’s important to have a predetermined methodology to ensure adoption is as high as possible. This can be done via:
- Developing training plans
- Assigning leadership groups and project champions
- Gamification of platform use and training programs
A thorough reverse approval process should also occur at the end of the project to ensure key deliverables have been met and communicated across the business, and that efficiencies, cost savings and ease-of-use are all widely understood.